What is a Cloud Security Architecture Assessment?
Providing data access from anywhere is the number one reason for cloud adoption by organisations today — unfortunately this makes cloud platforms a lucrative target for hackers and malicious entities.
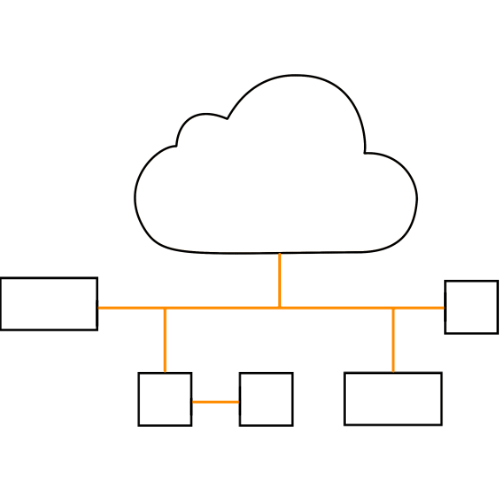
Many organisations operate in a hybrid manner, with dedicated links between on- premise infrastructure and that which resides in the cloud.
In the event where an organisation’s cloud service is compromised, it is not uncommon for the attacker to have a direct path into the organisation’s internal network.
To help organisations combat the threat of unauthorised access spiralling out of control, we offer our Cloud Security Architecture Assessment service where we undertake a detailed design review of the environment to identify weak points and offer suggestions where the network topology could be strengthened.
- The global public cloud computing market is set to exceed US$330 billion in 2020 and exceed US$623 billion by 2023.
- Hybrid cloud adoption is at 58% as of 2019.
- Through 2022, at least 95% of cloud security failures are predicted to be the cloud tenant’s fault.
- An average of 51% of organizations publicly exposed at least one cloud storage service.
- Privacy, security and lack of staff training are the top roadblocks to cloud adoption.
Why Choose Aurian?
Aurian consultants are highly experienced in both Amazon and Microsoft cloud platforms.
At each step of the assessment, our consultants will assess your cloud and/or hybrid network architecture in the context of your business requirements, offering solutions that allow you to operate your business but still ensure that you are meeting your security and compliance requirements.
Our Cloud Security Architecture Review will look at problematic security areas such as:
- Validating your current security policies, compliance and practices.
- Assessing the current firewall and security group policies.
- Identifying common misconfigurations such as allowing DNS to traverse between separate trust zones
- Determining unintended access paths to internal network resources in hybrid environments
- Reviewing current access control management and practices